
najszybciej rozwijających się rynków
transakcji dziennie
przeprocesowanych płatności e-commerce rocznie
pożyczek i rat online
inwestycji w fintech

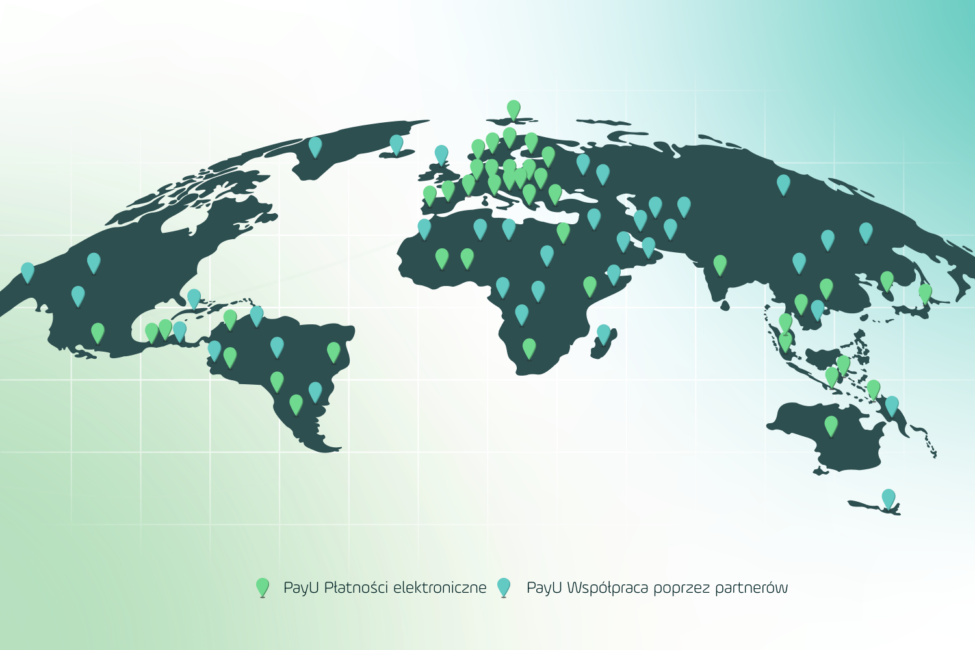
Oferujemy alternatywne metody płatności, jak również krajowe przetwarzanie płatności dzięki hiperlokalnym i bezpośrednim połączeniom z agentami rozliczeniowymi. Pomagamy również w realizacji płatności transgranicznych (cross-border e-commerce) i wspieramy naszych klientów w międzynarodowej ekspansji.

Pracujemy na rynkach, które stanowią bazę niemal 2,3 mld potencjalnych klientów i dają ogromne możliwości rozwoju w e-commerce. Pozwalamy użytkownikom, którzy nie mogą skorzystać z usług tradycyjnych banków, uzyskać dostęp do produktów kredytowych w sposób, który im odpowiada.

Rozumiemy indywidualne potrzeby biznesowe wielu branż. Obsługujemy podmioty różnej wielkości, działające w e-commerce, w sektorze finansowym czy usługowym na całym świecie, jednocześnie będąc jednym z największych inwestorów w przestrzeni FinTech z ponad $1 mld zainwestowanych w ciągu nieco ponad 3 lat.

98% klientów jest bardzo zadowolonych z usług PayU GPO, a aż 80% z nich zarekomendowałoby PayU GPO swoim znajomym. Sklepy internetowe w Polsce doceniają bezpieczeństwo transakcji, które zapewnia system PayU GPO – bezpieczeństwo procesowanych transakcji jest najważniejszą wartością dla 71% klientów PayU GPO.

Odpowiadamy za obszar FinTech i e-płatności w ramach Prosus, globalnej internetowej grupy konsumenckiej i jednego z największych inwestorów technologicznych na świecie, co wraz z zespołem najlepszych specjalistów napędza nasz wzrost i sukces każdego dnia.

Nasz system możesz połączyć ze swoim sklepem internetowym dzięki przygotowanym przez nas wtyczkom. Dodatkowo wiele popularnych platform SaaS to nasi partnerzy, którzy oferują gotową integrację z PayU GPO. Znajdź rozwiązanie najlepiej dopasowane do potrzeb Twojego e-commerce.

W PayU GPO, kultywując ideę transformacji i wzrostu, jesteśmy dumni z tego, że umożliwiamy e-biznesom rozwój w skali globalnej. Nasze zaangażowanie w zwiększanie ich doskonałości operacyjnej, napędzane jest przekonaniem, że sukcesy klientów są prawdziwą miarą naszych osiągnięć.
W każdym aspekcie naszej działalności, od najnowocześniejszej technologii po pełen pasji zespół ekspertów, dążymy do zapewnienia wyjątkowego doświadczenia, które wykracza poza wykonywane transakcje. Naszym celem jest bycie strategicznym partnerem naszych klientów, zapewniającym wartościową wiedzę i wsparcie w poruszaniu się po dynamicznym świecie globalnych płatności oraz w rozwijaniu ich biznesów.

PayU GPO i Siepomaga uruchamiają mikrodonacje
Czytaj dalej
Ceneo.pl wprowadza raty 5×0% od PayU
Czytaj dalej
Partnerstwo PayU i Klarny. Odroczone płatności trafią do kolejnych sklepów
Czytaj dalej
Integracja PayU GPO z platformą Mastercard Send
Czytaj dalej
Erli i PayU GPO rozszerzają współpracę partnerską
Czytaj dalej
Natychmiastowe przelewy na karty na Zrzutka.pl
Czytaj dalej
Nowe raty PayU: 5×0%!
Czytaj dalej
Najnowsze dane o branży fintech
Czytaj dalejMożesz w dowolnym momencie sprawdzić, czy Twoja wpłata została już przekazana odbiorcy. Wystarczy, że podasz datę, kwotę oraz numer transakcji lub adres e-mail.